First came the attack on Alaska’s court system in late April.
Hackers forced officials to shut down Alaska’s CourtView system for weeks, severing the public’s access to online court records and court filings. Access to the agency’s email was also closed off to people outside the court system.
Then, in May, hackers targeted Alaska’s state health department.
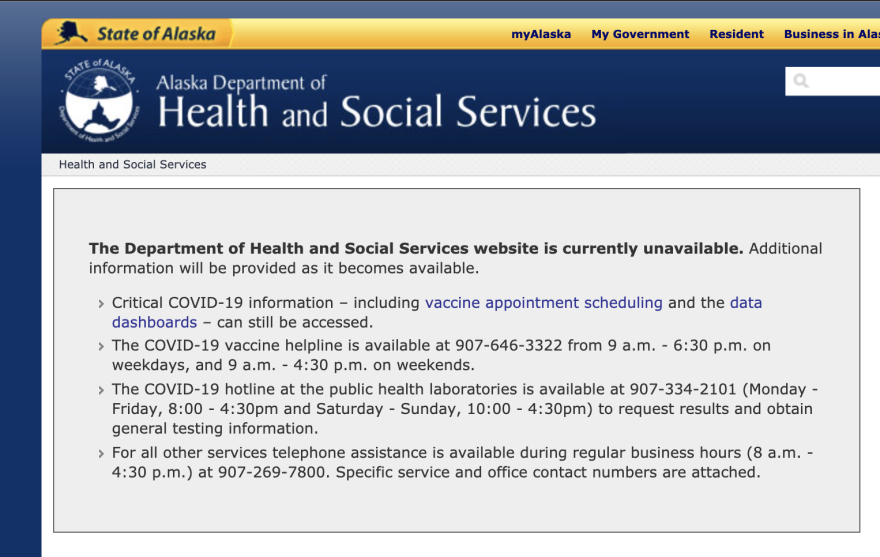
The Department of Health and Social Services’ website was taken offline, along with online services like vital records and a background check system.
The website remains offline today. And officials say several sections and divisions inside the agency are still contending with changes to their workflow, and relying on temporary web pages to reach the public.
So, what’s going on?
State officials have revealed few specifics about the attacks — particularly about the one that targeted the health department. They’ve also declined to release many details about the cyber-defenses they use to protect Alaska’s computer systems, and how they plan to adapt them to ensure that future attacks are less disruptive.
While there are still many unanswered questions, here’s what we've learned about the recent cyberattacks — and what we still don't know.
Who broke into the computer systems of Alaska’s court system and health department, and how did they do it?
These are the most obvious questions about the cyberattacks — and we don’t have answers to them. The health department, in a statement from spokesman Clinton Bennett, said it’s not releasing information “regarding the type of cyberattack, how the cyberattack occurred or other specific information.”
The court system’s top spokesman, Chief Justice Joel Bolger, has said a half-dozen computers were infected with malware that was trying to allow “outside actors” to move around the agency’s network. But in an interview Wednesday, he said those actors were never identified.
“We did not receive any direct communication from them,” he said.
Related: Amid cyberattacks, Alaska’s top cybersecurity official quietly left his job
Bolger said the unusual activity on the agency’s network was detected in late April by “cybersecurity notification software,” and that it was identified at an “early stage, before any of our computers had been taken over, locked up, encrypted — none of that stuff happened.” Two days after the discovery, the court system took its computer networks offline, to cut off the attackers’ access.
Bolger declined to say exactly how the hackers gained access to the court system’s network, stressing that he does not want to reveal information that could compromise his agency’s security in the future. He cited a recent ProPublica story that referred to one of the “cardinal rules of the cat-and-mouse game of cyber-warfare: Don’t let your opponents know what you’ve figured out.”
“I have had to be guarded on this issue to protect the integrity of the court system,” he said.
Did the hackers make any ransom or other demands of the state?
Bennett, from the health department, declined to answer the question.
In the court system’s case, officials say no ransom or other type of demand was made, and none was paid. Bolger also said that as far as his agency knows, no personal data nor sensitive data was stolen from its computers.
One interesting thing we learned: Alaska does not have any kind of statewide cybersecurity insurance policy. That’s a tool that some public entities and businesses — including the Anchorage's city government — use to lessen their losses from attacks, though prices have been rising recently. Until now, each agency has “dealt with the issue themselves,” said Dave Donley, a spokesman for the Department of Administration, which includes the state’s Office of Information Technology.
“Division of Risk Management has raised the question, and Office of Information Technology is considering options,” Donley wrote in an email.
How are the attacks being investigated?
The health department has not released any details about its investigation, though it said in a statement earlier this month that it’s analyzing the attack with law enforcement and state and federal partners. We also learned through a public records request that, following the attack, the health department hired Mandiant, a leading cybersecurity firm, with the cost estimated at $460,000.
The court system has said that federal and state law enforcement authorities were notified about the attack on that agency, and it’s also said it worked with a security consultant, though it hasn’t said which one, nor how much it paid.
While neither the court system nor the health department specifically confirmed its involvement, the FBI is the law enforcement agency that handles most Alaska-based cybersecurity investigations. The agency has a team of cyber-investigators at its Anchorage office that’s well-respected in Alaska’s IT community, and its agents have worked on a number of high-profile cases. Those include investigations targeting what are known as “botnets” — massive networks of computers or devices that have been hijacked by hackers.
"While the FBI does not confirm or deny the existence of investigations, when we learn of an intrusion, generally, it’s common for the FBI to offer assistance in determining its source and if there is a continuing threat," spokeswoman Chloe Martin said when asked about the attacks on the Alaska state agencies. "Similarly, the FBI routinely advises the public and private sectors about cyber threats in order to help them guard against the actions of cyber criminals."
What is the state doing to improve its cyberdefenses?
This is a key question, as cyberattacks against Alaska’s government aren’t expected to decrease any time soon.
Earlier this month, the health department said in a statement that it’s working to strengthen its people, processes and tools to make its computer systems more resilient to cyberattacks. But it added that the agency's large size and complex computer infrastructure means that the process will take more time. It also has not released any details about its plans.
Officials from Gov. Mike Dunleavy’s office declined an interview request about the state’s cybersecurity plans. Spokesman Jeff Turner said the administration “takes cybersecurity very seriously” but referred questions to the administration department, which also refused an interview request. An administration department spokesman, Brent Wittmer, said in an email that the department’s Office of Information Technology is “actively assessing the state of Alaska cybersecurity infrastructure to ensure it is effective and secure against recent and similar incidents.”
The court system’s computer systems and cybersecurity infrastructure are separate from the executive branch’s, said Bolger, the chief justice. The recent attack has made the agency more sensitive to cybersecurity, and working with its technology contractors, "we will have further things that we will do to try to harden our defenses," he said.
Bolger did not want to get into specifics, but he shared a few relevant details. He said one of the first things the court system did after the attack was reset all of its 750 employees’ passwords. The agency is also going to boost its use of what’s known as “multi-factor authentication” — that means requiring more than one identity verification, like a password, to access systems.
Bolger said the attack also underscores the importance of keeping all of the court system’s hardware and software up to date.
“It’s just kind of a wake-up call, that we have to pay attention to every little detail,” he said.
Do we know anything about holes in the state’s existing cybersecurity infrastructure?
One thing that several technology experts pointed out: Alaska has seen significant turnover in its top technology jobs in recent years. That includes Alaska’s top cybersecurity official, Mark Breunig, who left his job just last month for a cybersecurity advisor position at the U.S. Department of Homeland Security, according to his LinkedIn profile.
The state also saw at least five people hold the job of chief information officer between 2018 and 2019, according to the tech news site StateScoop. That CIO position is politically appointed by the commissioner of administration, rather than union-protected. Technology experts say that could make it harder for the CIO to take some of the politically difficult or expensive steps needed to ensure the state’s cybersecurity.
We also know that the state has been trying to consolidate its technology functions since 2017, based on an administrative order issued by then-Gov. Bill Walker, an independent. Experts told us that centralization could boost the security of each state agency’s systems by making them more consistent and accountable. But the agencies, which were used to controlling their own computer and technology systems, sometimes resisted the effort, and the work of consolidation is unfinished, according to an undated informational page on the administration department's website. Bill Smith, Alaska’s current CIO, told a government technology news site last year that the effort was only one-third complete.
Kelly Tshibaka, who led the administration department and has touted its technology centralization, left that job in March to run for U.S. Senate. She didn’t respond to an emailed request for an interview.
Correction: This story originally said, inaccurately, that the FBI declined to comment.